Over the last 6 months we have been hard at work on what we believe is the future of enterprise information security, and today we’re excited to lift the curtain - to some extent - on our most recent development: 3CORESec ONE and 3CORESec MDR.
3CORESec ONE
When we first got together to establish our product lineup, one thing became clear. If we wanted to make a difference we would require significant development on tools and platforms that worked how we thought information security should work: in a unified experience, with minimal changes to client workloads, pricing that is adjusted to different size companies, the capability to grow without additional purchases or any additional rewiring, and an overall less is more approach.
After two years of building individual components for our products, and some of them finding their way to the public in the form of SaaS platforms (i.e. lawmaker.cloud and dtection.io), 3CORESec ONE is the platform that brings it all together under a single virtual roof.
As the gateway to our ecosystem, ONE will serve as the identity platform for all our products and services, providing a streamlined experience in accessing not only the platforms themselves (through single sign on), but also allow our customers to access general information about their service subscriptions, invoicing, schedule demos and contact our support, interact with a dedicated success manager and much more!
Integrating our existing platforms under ONE is something we're actively working on, however, for the time being, ONE is being released fully integrated with 3CORESec MDR with platforms such as Lawmaker soon to follow.
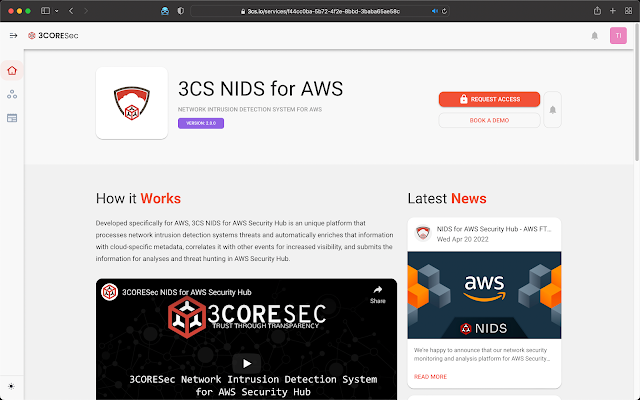
Example platform listing in 3CORESec ONE
3CORESec MDR
Our MDR portal is the culmination of almost 3 years of hard work in our unique detection capabilities, data-gathering software, innovative network traffic analyses appliances and all the bits and pieces that go together to provide a central, secure, tenant-aware application to observe, analyse, remediate and collaborate on cloud, network and endpoint.
The new MDR portal is currently in Beta and we are working hard to add more features, visualisations, collaboration and data interaction capabilities based, not only in our expertise, but also on client feedback.
3CORESec MDR - Network Findings Activity
3CORESec MDR uses a unique approach that provides our clients the ease of use of a SaaS platform while maintaining all the benefits of an internal/self-hosted solution. This allows for fast access to the platform, easy collaboration, quick onboarding and scaling and much more, while enjoying the peace of mind of siloed and secure data storage.
If you'd like to know more about our Managed Detection & Response platform, please contact us through social media or using the contact information available in our website.
The Future
The release of both these platforms is a new chapter for everyone at 3CORESec. It’s the start of a journey to provide the best experience for our users and we're excited for what's ahead.
Make sure to follow us on Twitter or LinkedIn to stay in the loop of all the exciting things we have coming. You can also join our Community Slack to hang out with us and, if you're interested in joining the team, we're hiring for all sorts of different positions (front/backend developers, threat researchers, system engineers, detection engineering, etc).
If you like what we're doing and want to make a difference in infosec, hit us up! 🤙🏼